 The difference between FTP and SFTP Protocol:
The difference between FTP and SFTP Protocol:
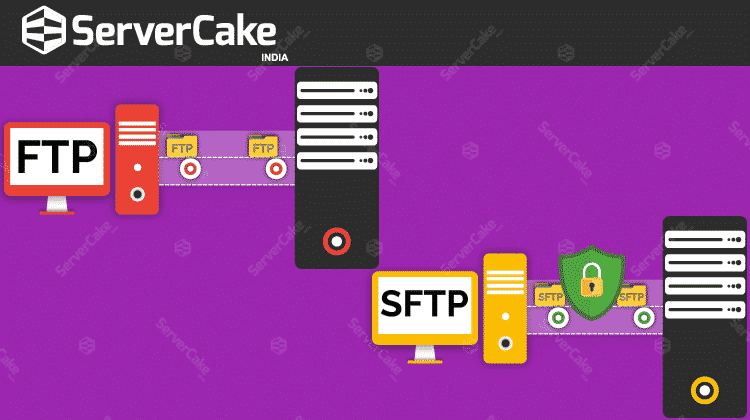
The major difference between FTP and SFTP is that when files are sent and received using “standard” FTP, they are done in an unencrypted appearance. This means that even though the connection itself may be secure, the transmission is not. Any data that is currently in transit can potentially be intercepted and read by a person with harmful intentions.
Encryption
FTP:
There are encrypted extensions to the FTP protocol that adds in-transit encryption using SSL (secure socket layer). These include Implicit FTPS and Explicit FTPS, both of which are essentially FTP-over-SSL.
SFTP:
SFTP also provides in-transit encryption by using SSH encryption instead of SSL encryption. Even if a packet of information was intercepted with SFTP or FTPS, the data inside would remain safe.
Firewalls
FTP:
FTP protocol uses one channel port 21 for sending commands and receiving acknowledgments. FTP (and FTPS) need to open other channels dynamically to send files. Though the client and server software will agree with those channels automatically, this poses an issue for client-side firewalls because many ports need to be open to the server’s IP address for the protocol to operate through the firewall without any interruption.
SFTP:
SFTP is a required single port (22) which is to be open for sending controls and for sending or receiving data files. SFTP and FTPS are uniformly secure from an encryption standpoint, but SFTP is a better choice to simplify firewall configurations. It is friendly to today’s client-side firewall.
FTP Vulnerabilities
FTP is absolutely a helpful and loyal method for file sharing. FTP does leave a lot to be desired for organizations that require a broad level of cyber security. For instance, the username and password information of the account currently transferring or accessing files is transmitted in plain text in FTP. Someone with the right tools and a little bit of knowledge can identify the information which could be intercepted, compromising not only the files on the FTP server but any other mission-critical account that uses that same identifying information. As already noted, using FTPS vs. FTP would reduce this issue, however since the protocol is basically identical, it is still possible for FTPS to use an unencrypted control channel.
SFTP does not contain a choice of an unencrypted control or data channel, and so by default, it does not broadcast any information in clear text. This adds an additional layer of security to a business operating in the digital realm. The other vulnerability is that there is a possibility for transferred data to not necessarily arrive at the end computer to which it was intended. It also uses an encrypted type of fingerprint technology to first transmit host keys before any data transfer to take place.